Many of the small size and medium-size companies are struggling to have a well-designed cybersecurity policy on account to make sure the accomplishment of their efforts and approaches of cybersecurity. The lapse of cybersecurity policy would have resulted from so many causes, though often encompass very few sources to contribute with emerging policies, slow acceptance by management and organization, or else just an absence of awareness regarding the significance to have an operative website security programs.
It does not matter that you own a multi-national company or any small setup – which is just recently initiated, your any kind of business must necessitate cybersecurity policies. Those policies would be served to involve the personnel and boost the outcomes, as well as they are a must-have to keep your business running and upgraded. The policy of cybersecurity recognizes the rules along with processes in which every person is getting accessibility and making use of the resources and Info-Tech assets of the organization. So the question arises why an organization requires cybersecurity policies?
Basic Policies Every Organization Should Have
The main aim of those policies is addressing IT-related risks and applies the techniques on account to mitigate Info-Tech security susceptibilities. These policies also define the ways to keep recovering while a network interruption comes about. On the other side, those policies offer guiding lines to personnel regarding what they should do and what they do not. They are also defining which person gets the accessibility to what, and also what are the penalties in case a person doesn’t follow such rules. The following are the nine major policies which should own by every small or medium size organization.
Employee Awareness and Training Policy
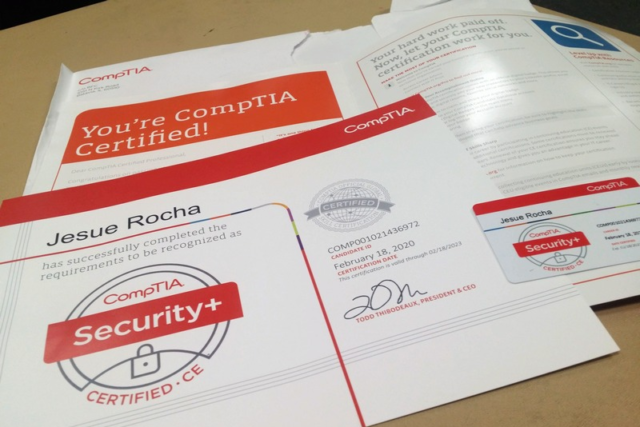
The most important thing is to train your staff – which is key to implement any of the cybersecurity policies. Your vigilance and training for valuable credentials, such as CompTIA Security+ certification training must provide learning to your workforces regarding the significance of IT-related security techniques in general when drawing training guidelines and awareness processes for every single policy – which is being followed.
Before roll out the newest security-related policies offers a sequence of in-person training sessions to the working staff, it may be in all hand pattern or else by a separate unit. This thing would guarantee that the personnel owns a chance to make aware of the actual policies, the reasons behind the implementation of those policies, and what effect the cybersecurity program gives towards the company.
Password Management Policy
Strong passcodes are an essential aspect in case you are hoping to maintain the sensitive data of your company protected and safe. The passcode policy of your business must teach staff the significance of original PINs; the ways to generate them, and how frequently to modify these passcodes.
Remote Access Policy
Since work from your home is relatively turn out to be the newest trend these days, remote data safety is more critical as compared to previous times. Because networking data would be interrupted with no trouble then a remote accessibility strategy (encompassing clear protocols for the system, computer, and V-P-N security) is vital to protect your customers, working staff, and the data and information of your company.
Permitted Access Policy
Intending to reduce manmade error (which is the main reason for data leakages), the entire businesses must be implementing an allowable accessibility policy. Keep in mind that employees must only attain an approach towards the info which is essential for their job – so that kind of policy has to be highlighted, document as well as limit the approach of personnel towards precise data and network.
Acceptable Use Policy
Talk about acceptable usages, like in what ways, at what place, and where your company’s tools are going to be implemented. When this policy is implemented, it must point out what it seems to be relevant usage of your organization’s computers, electronic mail, internet (as well as social media), customer and organization’s data, and many more, along with the penalties in case there is any misuse happens.
Regular Backup Policy
Malicious cyber attackers are always in a search to get accessibility to your organization’s information and then damage or steal it. You have to make sure regarding your data; it must be secured at any cost via daily planned backups of the data. Cloud resolutions are the perfect place to safely keep your data, mainly those hosted with the help of managed Info Tech services supplier.
Verify Legal Requirements
Depends on the varieties of data that you are managing, the place and authority of your company, and the company – which you’re operating, there might be fewer standards that must be implemented on account to making sure the security of your system as well as the reliability of your data. It’s mainly becoming true for the companies which are holding data that contains sensitive private info, just like credit card information, as well as social security numbers. In case your company is doing businesses with individuals or customers in the European – Union then, you should meet the terms with G-D-P-R.
Don’t Go Overboard
Relying on the outcomes of risk assessment then you must be enough capable to undoubtedly find the zones of Info-Tech risk and, therefore, cybersecurity’s level – which is suitable to your company. It’s not needed to apply too many security tools as they would give the side effect of hampering business processes.
Include Your Staff
Cybersecurity techniques are effective only in cases your working staff follows them. If not, you would be left regulating every other one. The main trick is to make sure that employees own buy-in and stake-in technique development. Make communications better also every year with the whole organization. Making sure that every staff member is acquiring why these rules should be developed, what are the threat, as well as the effects of a security event for the company and their personnel?
Wrap-Up
Irrespective of the size of the organization, it’s essential for each company to apply and follow the basic and crucial policies to save the data of an organization, as well as other valued assets. It becomes a necessity for the companies which should be following numerous regulations. The main aspect is to owe “documented” safety measures that describe your position of an organization on security.


Lastest Posts
Lifestyle
Big Game Hunting in The Iberian Mountains: Must-Visit Destinations for Hunters
Education
How machine translation is changing the industry: When to use it and when to avoid it?
Health
EEG Analysis: Technology Connecting the Brain to the Future
Marketing
Advancements in Solar Panel Technology: Illuminating the Path to a Sustainable Future
Lifestyle
How to Build a Capsule Wardrobe: Essentials for Every Man
Lifestyle
Women in the Catholic Church: Roles, Recognition, and Calls for Change
Marketing
Experiential Marketing for Brands: Crafting Unforgettable Consumer Connections